Enumeration is the first step you have to take once you gain access to any
system. You may have accessed the system by exploiting a critical
vulnerability that resulted in root-level access or just found a way to send
commands using a low privileged account. Penetration testing engagements,
unlike CTF machines, don't end once you gain access to a specific system or
user privilege level.
As you will see, enumeration is as important during
the post-compromise phase as it is before.
hostname
The hostname command will return the hostname of the target machine.
Although this value can easily be changed or have a
relatively
meaningless string (e.g. Ubuntu-3487340239), in some cases, it can provide
information about the target system’s
role within the corporate network
(e.g. SQL-PROD-01 for a production SQL server).
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ hostname
KumarAtulJaiswal
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
uname -a
Will print system information giving us additional detail about the
kernel used by the system. This will be useful when searching for any
potential kernel vulnerabilities that could lead to privilege escalation.
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ uname -a
Linux KumarAtulJaiswal 5.18.0-kali2-amd64 #1 SMP PREEMPT_DYNAMIC Debian 5.18.5-1kali1 (2022-06-20) x86_64 GNU/Linux
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
/proc/version
The proc filesystem (procfs) provides information about the target
system processes. You will find proc on many different Linux
flavours,
making it an essential tool to have in your arsenal.
Looking
at /proc/version may give you information on the kernel version and additional
data such as whether a compiler (e.g. GCC)
is installed.
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ cat /proc/version
Linux version 5.18.0-kali2-amd64 (devel@kali.org) (gcc-11 (Debian 11.3.0-3) 11.3.0, GNU ld (GNU Binutils for Debian) 2.38) #1 SMP PREEMPT_DYNAMIC Debian 5.18.5-1kali1 (2022-06-20)
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
/etc/issue
Systems can also be identified by looking at the /etc/issue file.
This file usually contains some information about the operating system but can
easily be customized or changes. While on the subject, any file containing
system information can be customized or changed. For a clearer understanding
of the system, it is always good to look at all of these.
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ cat /etc/issue
Kali GNU/Linux Rolling \n \l
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
ps Command
The ps command is an effective way to see the running processes on a
Linux system. Typing ps on your terminal will show processes for the current
shell.
The output of the ps (Process Status) will show the
following:
- PID: The process ID (unique to the process)
- TTY: Terminal type used by the user
-
Time: Amount of CPU time used by the process (this is NOT the time this
process has been running for)
-
CMD: The command or executable running (will NOT display any command line
parameter)
The “ps” command provides a few useful options.
- ps -A: View all running processes
-
ps axjf: View process tree (see the tree formation until ps axjf is run
below)
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ ps aux
USER PID %CPU %MEM VSZ RSS TTY STAT START TIME COMMAND
root 1 0.0 0.2 167472 9832 ? Ss 11:06 0:02 /sbin/init splash
root 2 0.0 0.0 0 0 ? S 11:06 0:00 [kthreadd]
root 3 0.0 0.0 0 0 ? I< 11:06 0:00 [rcu_gp]
root 4 0.0 0.0 0 0 ? I< 11:06 0:00 [rcu_par_gp]
root 5 0.0 0.0 0 0 ? I< 11:06 0:00 [netns]
root 7 0.0 0.0 0 0 ? I< 11:06 0:00 [kworker/0:0H-events_highpri]
root 9 0.0 0.0 0 0 ? I< 11:06 0:02 [kworker/0:1H-events_highpri]
root 10 0.0 0.0 0 0 ? I< 11:06 0:00 [mm_percpu_wq]
root 11 0.0 0.0 0 0 ? I 11:06 0:00 [rcu_tasks_kthread]
root 12 0.0 0.0 0 0 ? I 11:06 0:00 [rcu_tasks_rude_kthread]
root 13 0.0 0.0 0 0 ? I 11:06 0:00 [rcu_tasks_trace_kthread]
root 14 0.0 0.0 0 0 ? S 11:06 0:01 [ksoftirqd/0]
root 15 0.1 0.0 0 0 ? I 11:06 0:22 [rcu_preempt]
root 16 0.0 0.0 0 0 ? S 11:06 0:00 [migration/0]
env
The env command will show environmental variables.
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ env
COLORFGBG=15;0
COLORTERM=truecolor
COMMAND_NOT_FOUND_INSTALL_PROMPT=1
DBUS_SESSION_BUS_ADDRESS=unix:path=/run/user/1000/bus
DESKTOP_SESSION=lightdm-xsession
DISPLAY=:0.0
DOTNET_CLI_TELEMETRY_OPTOUT=1
GDMSESSION=lightdm-xsession
GDM_LANG=en_IN.utf8
GTK_MODULES=gail:atk-bridge
HOME=/home/hackerboy
LANG=en_IN
LANGUAGE=en_IN:en
LOGNAME=hackerboy
PANEL_GDK_CORE_DEVICE_EVENTS=0
PATH=/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/local/games:/usr/games
POWERSHELL_TELEMETRY_OPTOUT=1
POWERSHELL_UPDATECHECK=Off
PWD=/home/hackerboy
QT_ACCESSIBILITY=1
QT_AUTO_SCREEN_SCALE_FACTOR=0
QT_QPA_PLATFORMTHEME=qt5ct
SESSION_MANAGER=local/KumarAtulJaiswal:@/tmp/.ICE-unix/1092,unix/KumarAtulJaiswal:/tmp/.ICE-unix/1092
SHELL=/usr/bin/zsh
SSH_AGENT_PID=1147
SSH_AUTH_SOCK=/tmp/ssh-XXXXXXAg7KOV/agent.1092
TERM=xterm-256color
USER=hackerboy
WINDOWID=0
XAUTHORITY=/home/hackerboy/.Xauthority
XDG_CONFIG_DIRS=/etc/xdg
XDG_CURRENT_DESKTOP=XFCE
XDG_DATA_DIRS=/usr/share/xfce4:/usr/local/share/:/usr/share/:/usr/share
XDG_GREETER_DATA_DIR=/var/lib/lightdm/data/hackerboy
XDG_MENU_PREFIX=xfce-
XDG_RUNTIME_DIR=/run/user/1000
XDG_SEAT=seat0
XDG_SEAT_PATH=/org/freedesktop/DisplayManager/Seat0
XDG_SESSION_CLASS=user
XDG_SESSION_DESKTOP=lightdm-xsession
XDG_SESSION_ID=3
XDG_SESSION_PATH=/org/freedesktop/DisplayManager/Session0
XDG_SESSION_TYPE=x11
XDG_VTNR=7
_JAVA_OPTIONS=-Dawt.useSystemAAFontSettings=on -Dswing.aatext=true
SHLVL=1
OLDPWD=/home/hackerboy
LS_COLORS=rs=0:di=01;34:ln=01;36:mh=00:pi=40;33:so=01;35:do=01;35:bd=40;33;01:cd=40;33;01:or=40;31;01:mi=00:su=37;41:sg=30;43:ca=30;41:tw=30;42:ow=34;42:st=37;44:ex=01;32:*.tar=01;31:*.tgz=01;31:*.arc=01;31:*.arj=01;31:*.taz=01;31:*.lha=01;31:*.lz4=01;31:*.lzh=01;31:*.lzma=01;31:*.tlz=01;31:*.txz=01;31:*.tzo=01;31:*.t7z=01;31:*.zip=01;31:*.z=01;31:*.dz=01;31:*.gz=01;31:*.lrz=01;31:*.lz=01;31:*.lzo=01;31:*.xz=01;31:*.zst=01;31:*.tzst=01;31:*.bz2=01;31:*.bz=01;31:*.tbz=01;31:*.tbz2=01;31:*.tz=01;31:*.deb=01;31:*.rpm=01;31:*.jar=01;31:*.war=01;31:*.ear=01;31:*.sar=01;31:*.rar=01;31:*.alz=01;31:*.ace=01;31:*.zoo=01;31:*.cpio=01;31:*.7z=01;31:*.rz=01;31:*.cab=01;31:*.wim=01;31:*.swm=01;31:*.dwm=01;31:*.esd=01;31:*.jpg=01;35:*.jpeg=01;35:*.mjpg=01;35:*.mjpeg=01;35:*.gif=01;35:*.bmp=01;35:*.pbm=01;35:*.pgm=01;35:*.ppm=01;35:*.tga=01;35:*.xbm=01;35:*.xpm=01;35:*.tif=01;35:*.tiff=01;35:*.png=01;35:*.svg=01;35:*.svgz=01;35:*.mng=01;35:*.pcx=01;35:*.mov=01;35:*.mpg=01;35:*.mpeg=01;35:*.m2v=01;35:*.mkv=01;35:*.webm=01;35:*.webp=01;35:*.ogm=01;35:*.mp4=01;35:*.m4v=01;35:*.mp4v=01;35:*.vob=01;35:*.qt=01;35:*.nuv=01;35:*.wmv=01;35:*.asf=01;35:*.rm=01;35:*.rmvb=01;35:*.flc=01;35:*.avi=01;35:*.fli=01;35:*.flv=01;35:*.gl=01;35:*.dl=01;35:*.xcf=01;35:*.xwd=01;35:*.yuv=01;35:*.cgm=01;35:*.emf=01;35:*.ogv=01;35:*.ogx=01;35:*.aac=00;36:*.au=00;36:*.flac=00;36:*.m4a=00;36:*.mid=00;36:*.midi=00;36:*.mka=00;36:*.mp3=00;36:*.mpc=00;36:*.ogg=00;36:*.ra=00;36:*.wav=00;36:*.oga=00;36:*.opus=00;36:*.spx=00;36:*.xspf=00;36:
LESS_TERMCAP_mb=
LESS_TERMCAP_md=
LESS_TERMCAP_me=
LESS_TERMCAP_so=
LESS_TERMCAP_se=
LESS_TERMCAP_us=
LESS_TERMCAP_ue=
_=/usr/bin/env
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
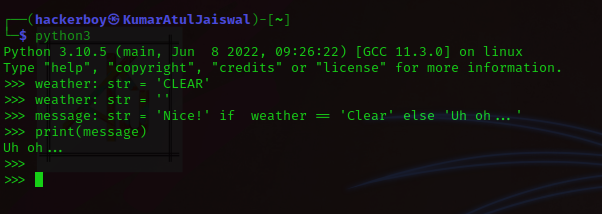
The PATH variable may have a compiler or a scripting
language (e.g. Python) that could be used to run code on the target system or leveraged for
privilege escalation.
sudo -l
The target system may be configured to allow users to run some (or all)
commands with root privileges. The sudo -l command can be
used to list
all commands your user can run using sudo.
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ sudo -l
[sudo] password for hackerboy:
Matching Defaults entries for hackerboy on KumarAtulJaiswal:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, use_pty
User hackerboy may run the following commands on KumarAtulJaiswal:
(ALL : ALL) ALL
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
ls
One of the common commands used in Linux is probably ls.
While looking for potential privilege escalation vectors,
please remember to always use the ls command with the -la parameter.
The
example below shows how the “secret.txt” file can easily be missed using the
ls or ls -l commands.
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$ ls
check.txt id_rsa.txt
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$ ls -la
total 24
drwxr-xr-x 2 hackerboy hackerboy 4096 May 11 2022 .
drwxr-xr-x 138 hackerboy hackerboy 12288 Dec 27 14:35 ..
-rwxrwxrwx 1 hackerboy hackerboy 666 Oct 15 2020 check.txt
-rwxrwxrwx 1 hackerboy hackerboy 1674 Oct 15 2020 id_rsa.txt
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$
Id
The id command will provide a general overview of the user’s privilege
level and group memberships.
It is worth remembering that the id command
can also be used to obtain the same information for another user as seen
below.
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$ id
uid=1000(hackerboy) gid=1000(hackerboy) groups=1000(hackerboy),20(dialout),24(cdrom),25(floppy),27(sudo),29(audio),30(dip),44(video),46(plugdev),109(netdev),119(bluetooth),121(wireshark),134(scanner),142(kaboxer)
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$
/etc/passwd
Reading the /etc/passwd file can be an easy way to discover users on the
system.
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$ cat /etc/passwd
root:x:0:1:root:/root:/usr/bin/zsh
daemon:x:1:0:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:0:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
While the output can be long and a bit intimidating, it can easily be cut and
converted to a useful list for brute-force attacks.
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$ cat /etc/passwd | cut -d ":" -f 1
root
daemon
bin
sys
sync
games
man
lp
Remember that this will return all users, some of which are system or service
users that would not be very useful. Another approach could be to grep for
“home” as real users will most likely have their folders under the “home”
directory.
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$ cat /etc/passwd | grep home
hackerboy:x:1000:1000:hackerboy,,,:/home/hackerboy:/usr/bin/zsh
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$
history
Looking at earlier commands with the history command can give us some
idea about the target system and, albeit rarely,
have stored information
such as passwords or usernames.
ifconfig
The target system may be a pivoting point to another network. The
ifconfig command will give us information about the network
interfaces of
the system. The example below shows the target system has three interfaces
(eth0, tun0, and tun1). Our attacking
machine can reach the eth0
interface but can not directly access the two other networks.
This can be confirmed using the
ip route command to see which network routes exist.
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$ ip route
default via 192.168.13.125 dev usb0 proto dhcp src 192.168.13.51 metric 100
192.168.13.0/24 dev usb0 proto kernel scope link src 192.168.13.51 metric 100
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/wgel]
└─$
netstat
Following an initial check for existing interfaces and network
routes, it is worth looking into existing communications. The
netstat command can be used with several different options to
gather information on existing connections.
-
netstat -a: shows all listening ports and established connections.
-
netstat -at or netstat -au can also be used to list TCP or UDP
protocols respectively.
-
netstat -l: list ports in “listening” mode. These ports are open and
ready to accept incoming connections. This can be used with the “t” option
to list only ports that are listening using the TCP protocol (below).
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ netstat -lt
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State
tcp 0 0 0.0.0.0:ssh 0.0.0.0:* LISTEN
tcp6 0 0 [::]:ssh [::]:* LISTEN
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
netstat -s: list network usage statistics by protocol (below) This can
also be used with the -t or -u options to limit the output to a specific
protocol.
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ netstat -s
Ip:
Forwarding: 2
32791 total packets received
2 with invalid addresses
0 forwarded
0 incoming packets discarded
32782 incoming packets delivered
29047 requests sent out
Icmp:
0 ICMP messages received
0 input ICMP message failed
ICMP input histogram:
0 ICMP messages sent
0 ICMP messages failed
ICMP output histogram:
Tcp:
423 active connection openings
0 passive connection openings
2 failed connection attempts
2 connection resets received
10 connections established
21178 segments received
20463 segments sent out
94 segments retransmitted
4 bad segments received
674 resets sent
Udp:
11606 packets received
0 packets to unknown port received
0 packet receive errors
10177 packets sent
0 receive buffer errors
0 send buffer errors
UdpLite:
TcpExt:
184 TCP sockets finished time wait in fast timer
2 packetes rejected in established connections because of timestamp
213 delayed acks sent
Quick ack mode was activated 33 times
9166 packet headers predicted
1752 acknowledgments not containing data payload received
1803 predicted acknowledgments
TCPSackRecovery: 3
Detected reordering 14 times using SACK
1 congestion windows fully recovered without slow start
TCPDSACKUndo: 2
TCPLostRetransmit: 1
3 fast retransmits
TCPTimeouts: 11
TCPLossProbes: 82
TCPLossProbeRecovery: 10
TCPDSACKOldSent: 33
TCPDSACKOfoSent: 12
TCPDSACKRecv: 45
94 connections reset due to unexpected data
2 connections reset due to early user close
TCPDSACKIgnoredNoUndo: 24
TCPSackShiftFallback: 31
TCPRcvCoalesce: 4786
TCPOFOQueue: 5029
TCPOFOMerge: 12
TCPChallengeACK: 4
TCPSYNChallenge: 4
TCPAutoCorking: 38
TCPSynRetrans: 9
TCPOrigDataSent: 5683
TCPHystartDelayDetect: 1
TCPHystartDelayCwnd: 320
TCPACKSkippedPAWS: 1
TCPKeepAlive: 292
TCPDelivered: 5862
TCPAckCompressed: 1018
TCPDSACKRecvSegs: 45
IpExt:
InOctets: 34605350
OutOctets: 14722497
InNoECTPkts: 32749
InECT0Pkts: 42
MPTcpExt:
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
netstat -tp: list connections with the service name and PID
information.
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ netstat -tp
(Not all processes could be identified, non-owned process info
will not be shown, you would have to be root to see it all.)
Active Internet connections (w/o servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 192.168.63.167:34046 bom12s20-in-f9.1e:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:50054 server-18-161-111:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:55010 bom12s20-in-f9.1e:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:48406 233.90.160.34.bc.:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:38404 ec2-35-174-127-31:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:43460 104.22.54.228:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:32888 104.22.54.228:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:43446 104.22.54.228:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:44862 ec2-3-225-70-247.:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:38596 bom12s20-in-f9.1e:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:36350 ec2-100-20-114-17:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:57030 201.181.244.35.bc:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:50894 23.58.120.34.bc.g:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:58606 104.22.54.228:https ESTABLISHED 1803/firefox-esr
tcp 0 0 192.168.63.167:34198 ec2-35-174-127-31:https ESTABLISHED 1803/firefox-esr
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
This can also be used with the -l option to list listening ports
(below)
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ netstat -ltp
(Not all processes could be identified, non-owned process info
will not be shown, you would have to be root to see it all.)
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:ssh 0.0.0.0:* LISTEN -
tcp6 0 0 [::]:ssh [::]:* LISTEN -
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
We can see the “PID/Program name” column is empty as this process is
owned by another user.
Below is the same command run with root
privileges and reveals this information as 2641/nc (netcat)
netstat -i: Shows interface statistics. We see below that “eth0”
and “tun0” are more active than “tun1”
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ netstat -i
Kernel Interface table
Iface MTU RX-OK RX-ERR RX-DRP RX-OVR TX-OK TX-ERR TX-DRP TX-OVR Flg
eth0 1500 0 0 0 0 0 0 0 0 BMU
lo 65536 4 0 0 0 4 0 0 0 LRU
usb0 1500 36151 0 0 0 38299 0 0 0 BMRU
wlan0 1500 0 0 0 0 0 0 0 0 BMU
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
The netstat usage you will probably see most often in blog posts, write-ups,
and courses is netstat -ano which could be broken down as follows;
- -a: Display all sockets
- -n: Do not resolve names
- -o: Display timers
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ netstat -ano
Active Internet connections (servers and established)
Proto Recv-Q Send-Q Local Address Foreign Address State Timer
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN off (0.00/0/0)
tcp 0 0 192.168.63.167:50054 18.161.111.125:443 TIME_WAIT timewait (4.61/0/0)
tcp 0 0 192.168.63.167:55010 142.251.42.41:443 ESTABLISHED off (0.00/0/0)
tcp 0 0 192.168.63.167:48406 34.160.90.233:443 TIME_WAIT timewait (5.55/0/0)
find Command
Searching the target system for important information and potential
privilege escalation vectors can be fruitful. The built-in “find” command is
useful and worth keeping in your arsenal.
Below are some useful
examples for the “find” command.
Find files:
-
find . -name flag1.txt: find the file named
“flag1.txt” in the current directory
-
find /home -name flag1.txt: find the file names
“flag1.txt” in the /home directory
-
find / -type d -name config: find the directory
named config under “/”
-
find / -type f -perm 0777: find files with the 777
permissions (files readable, writable, and executable by all users)
- find / -perm a=x: find executable files
-
find /home -user frank: find all files for user
“frank” under “/home”
-
find / -mtime 10: find files that were modified in
the last 10 days
-
find / -atime 10: find files that were accessed in
the last 10 day
-
find / -cmin -60: find files changed within the
last hour (60 minutes)
-
find / -amin -60: find files accesses within the
last hour (60 minutes)
-
find / -size 50M: find files with a 50 MB size
This command can also be used with (+) and (-) signs to
specify a file that is larger or smaller than the given size.
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ find / -size +100M
/home/hackerboy/Videos/3.mp4
/home/hackerboy/.local/share/torbrowser/tbb/x86_64/tor-browser_en-US/Browser/libxul.so
/home/hackerboy/Documents/OSCP-machine/Hack_Me_Please.rar
/home/hackerboy/Documents/OSCP-machine/Ubuntu_CTF.ova
/home/hackerboy/Documents/sql/rockyou.txt
/home/hackerboy/Documents/iMaHackerBoY/new/osf.exe
/home/hackerboy/Documents/iMaHackerBoY/new/Hacking-All-books-PDF/Nmap Network Scanning_ The Official Nmap Project Guide to Network Discovery and Security Scanning ( PDFDrive.com ).pdf
find: ‘/proc/3159/ns’: Permission denied
find: ‘/proc/3166/task/3166/fd’: Permission denied
find: ‘/proc/3166/task/3166/fdinfo’: Permission denied
find: ‘/proc/3166/task/3166/ns’: Permission denied
find: ‘/proc/3166/fd’: Permission denied
find: ‘/proc/3166/map_files’: Permission denied
find: ‘/proc/3166/fdinfo’: Permission denied
find: ‘/proc/3166/ns’: Permission denied
find: ‘/proc/3221/task/3221/fd’: Permission denied
find: ‘/proc/3221/task/3221/fdinfo’: Permission denied
find: ‘/proc/3221/task/3221/ns’: Permission denied
find: ‘/proc/3221/fd’: Permission denied
find: ‘/proc/3221/map_files’: Permission denied
find: ‘/proc/3221/fdinfo’: Permission denied
find: ‘/proc/3221/ns’: Permission denied
find: ‘/proc/3222/task/3222/fd’: Permission denied
find: ‘/proc/3222/task/3222/fdinfo’: Permission denied
find: ‘/proc/3222/task/3222/ns’: Permission denied
find: ‘/proc/3222/fd’: Permission denied
find: ‘/proc/3222/map_files’: Permission denied
find: ‘/proc/3222/fdinfo’: Permission denied
find: ‘/proc/3222/ns’: Permission denied
find: ‘/proc/3316/task/3316/fd/5’: No such file or directory
find: ‘/proc/3316/task/3316/fdinfo/5’: No such file or directory
find: ‘/proc/3316/fd/6’: No such file or directory
find: ‘/proc/3316/fdinfo/6’: No such file or directory
find: ‘/.cache’: Permission denied
/usr/share/burpsuite/burpsuite.jar
The example above returns files that are larger than 100 MB. It is important
to note that the “find” command tends to generate errors which sometimes makes
the output hard to read. This is why it would be wise to use the “find”
command with “-type f 2>/dev/null” to redirect errors to “/dev/null”
and have a cleaner output (below).
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ find / -size +100M -type f 2>/dev/null
/home/hackerboy/Videos/3.mp4
/home/hackerboy/.local/share/torbrowser/tbb/x86_64/tor-browser_en-US/Browser/libxul.so
/home/hackerboy/Documents/OSCP-machine/Hack_Me_Please.rar
/home/hackerboy/Documents/OSCP-machine/Ubuntu_CTF.ova
/home/hackerboy/Documents/sql/rockyou.txt
/home/hackerboy/Documents/iMaHackerBoY/new/osf.exe
/home/hackerboy/Documents/iMaHackerBoY/new/Hacking-All-books-PDF/Nmap Network Scanning_ The Official Nmap Project Guide to Network Discovery and Security Scanning ( PDFDrive.com ).pdf
/home/hackerboy/Documents/iMaHackerBoY/new/kali/Nmap Network Scanning_ The Official Nmap Project Guide to Network Discovery and Security Scanning ( PDFDrive.com ).pdf
/home/hackerboy/Documents/rockyou.txt
/home/hackerboy/Documents/import/rainbow table/winrtgen/md5_alpha-numeric#1-7_0_2400x40000000_oxid#000.rt
/home/hackerboy/Documents/import/cerified website for CEH/Nmap Network Scanning_ The Official Nmap Project Guide to Network Discovery and Security Scanning ( PDFDrive.com ).pdf
Folders and files that can be written to or executed from:
-
find / -writable -type d 2>/dev/null : Find world-writeable folders
-
find / -perm -222 -type d 2>/dev/null: Find
world-writeable folders
-
find / -perm -o w -type d 2>/dev/null: Find
world-writeable folders
The reason we see three different “find” commands that could potentially
lead to the same result can be seen in the manual document. As you can see
below, the perm parameter affects the way “find” works.
-
find / -perm -o x -type d 2>/dev/null : Find
world-executable folders
Find development tools and supported languages:
- find / -name perl*
- find / -name python*
- find / -name gcc*
Find specific file permissions:
Below is a short example used
to find files that have the SUID bit set. The SUID bit allows the file to run
with the privilege level of the account that owns it, rather than the account
which runs it. This allows for an interesting privilege escalation path,we
will see in more details on task 6. The example below is given to complete the
subject on the “find” command.
-
find / -perm -u=s -type f 2>/dev/null: Find
files with the SUID bit, which allows us to run the file with a higher
privilege level than the current user.
General Linux Commands
As we are in the Linux realm, familiarity with Linux commands, in
general, will be very useful. Please spend some time getting comfortable with
commands such as find, locate, grep, cut, sort, etc.
Disclaimer
All tutorials are for informational and educational purposes only and have
been made using our own routers, servers, websites and other vulnerable free
resources. we do not contain any illegal activity. We believe that ethical
hacking, information security and cyber security should be familiar subjects
to anyone using digital information and computers. Hacking Truth is against
misuse of the information and we strongly suggest against it. Please regard
the word hacking as ethical hacking or penetration testing every time this
word is used. We do not promote, encourage, support or excite any illegal
activity or hacking.